Today’s institutional investors are wise to custody their digital assets with a trusted third party — but can you reduce risk even further by spreading your assets across multiple custodians?
In this blog, we invited you to explore two solutions—HSM vs MPC— for institutional crypto assets custody in real-time, we also added a third for your consideration - our Scalable HSM. We look at how each meets the demand for security and personal risk to the client.
The long-term capital growth prospects of cryptocurrencies and digital assets have seen institutional adoption on the rise. Institutional investors and service providers in crypto markets are going to need greater scale, flexibility and added security measures to build, run and operate a successful digital assets business in real-time with low latency.
However, security and risk mitigation practices in private key safekeeping for multi-user financial organisations are still a concern.
Even new and innovative technology like MPC is not immune to failure.
Recent news of some clients losing their keys or millions hacked due to vulnerabilities with an MPC wallet on Binance Smart Chain, all indicate that diversifying your custodian network to include tried and tested, may be more prudent in security and risk mitigation.
When it comes to cryptoasset key custody, expertise in the planning of risk controls and contingencies is of the utmost importance. Read on to understand what's best for your institution.
HSMs

Hardware security modules, HSMs, are dedicated computing devices designed for the safe storage and use of cryptographic keys. What makes them unique is the hardened nature of their operating system, libraries and the ability to wipe key material when they detect attempts to interfere with the device.
They have been long trusted by banks and payment networks, managing trillions of payments worldwide for over 30 years now, indicating decades of in-field deployment experience. They are not, however, without their downsides; complex to configure and program, hard to scale and with limited capacities, they can often not be the first choice in the face of alternative solutions.
MPC

Multi-party computation, MPC, is another long-standing technology, having been utilised as early as the 1970s.
Based on the ability to cooperatively compute the solution to a function while keeping each party's inputs secret, these algorithms have increasingly found favour in the world of blockchain and crypto assets in the last 5 years.
The cutting-edge mathematics that these algorithms are based on maybe intractable for most, but promise secure threshold key signing without any one party holding the entirety of the key (key sharding).
Some MPC providers, for instance, furnish the underlying infrastructure needed to provide custody, but take on a ‘shared or collaborative’ approach with their clients where they are in part custodians themselves responsible for the backup and recovery of their key shard.
Again, although this sounds great in theory, in practice they still come with challenges around ensuring that the key shards that each party holds are secure and resilient in the face of failure. Additionally, as the number of signatories increases, scalability becomes difficult.
Scalable HSM - A Higher Security Module That's Safer, Faster and Easier for Institutions
Bitpanda Custody is one of a handful of service providers using HSMs. But the devil is in the details. By re-signing transactions with our proprietary firmware running inside HSMs, we mitigate an important attack vector.
Whilst the HSM may keep the wallet key safe, and even if other providers also use some form of end-user hardware to authenticate transactions, hackers can still compromise the transaction if policy validation and re-signing are performed in software.
It is this unique re-signing technology that enables us to easily adapt to any signature schemes like BLS but also to different blockchains and protocols.
***************
"BItpanda Custody' digital asset management solutions have provided us with the comfort we need, particularly from a security and compliance perspective. The technical quality of their solutions, their favourable FCA positioning, and the collaborative disposition of their team all contribute to BItpanda Custody being an excellent enabler in a complex industry."Ciaran MacDevette, Co-Founder, Bakari AG
********************
To address the challenges of scale, Bitpanda Custody began by making each HSM device stateless; each customer wallet is generated securely inside one of our HSMs by our bespoke firmware, but then the key material is wrapped and backed up to the cloud when not in use to ensure resilience.
At the time of generating the wallet, we also attach a cryptographically signed policy that details the rules defining who can spend assets from the wallet and who can change the policy in the future.
Each signing operation is treated atomically, with the wrapped key material and signed policy data being sent back to any of our HSMs along with data to authenticate the transaction.
As long as at least one of our HSM devices is available then signing can proceed in less than one second.
The other facet of scaling is the limited storage on the HSM device. The above solution, where data is stored in the cloud, manages to mostly sidestep this issue, the only piece of data that each HSM stores in relation to a customer wallet is the current policy version number, preventing replaying of old policy data once it has been changed.
These capabilities have allowed us to scale to tens of thousands of wallets, each having an almost infinite number of keys within them while maintaining our sub-second signing capability.
Each HSM only needs to be commissioned with a minimal set of keys, symmetric keys for wrapping key material and asymmetric keys for signing policies and ensuring provenance, and new devices can be provisioned within a few hours.
The policies associated with wallets define which combination of client keys can be used to authenticate a transaction. These client keys, which are used to verify customer authenticity and have no algorithmic relationship to the custodied key material, are stored inside the iOS device secure enclave or alternative secure key store services like AWS Key Management Service or Azure Key Vault.
By leveraging these technologies we ensure hardware-based security across our entire service.
The Breakdown: Scalable HSM vs MPC
|
Scalable HSM |
MPC |
|
|
Removes single point of failure |
✓ |
✓ |
|
Enterprise-grade multi-layer security |
✓ |
✓ |
|
Easy to scale |
✓ |
✖ |
|
Protocol agnostic, low Ethereum fees |
✓ |
✓ |
|
Multi-user approval |
✓ |
✓ |
|
Client key-backup and recovery |
✓ |
✖ |
|
Key sharding |
✖ |
✓ |
|
Money-laundering regulation compliance |
✓ |
✖ |
|
Modify quorums without creating a new address |
✓ |
✓ |
|
Offline signing |
✖ |
✓ |
|
Hardware supported |
✓ |
✖ |
|
Deployable via cloud service or API |
✓ |
✓ |
|
Insurance coverage |
✓ |
✓ |
Concluding thoughts
In today's fast-paced, evolving crypto markets, it may be more prudent for institutions to diversify their custodian network to effectively manage security and risk.
A combination of tried and trusted technologies with solid multi-party processes (multiple custodians) can ensure institutions get the best of both worlds.
Bitpanda Custody has taken trusted HSM technology and scaled it for the blockchain age, ensuring resiliency and scalability for our customers’ signing needs, debunking the myth that HSM multi-sig solutions can no longer support the needs of institutional investors and service providers in crypto assets.
Our solution can meet any complex quorum rules, is protocol and blockchain agnostic and ensures any policies or rules set is met with our bespoke resigning technology firmware.
Custom integrations with MetaMask and WalletConnect enable secure access to any Ethereum based DeFi DApp today.
If you truly believe in "Not your keys, not your coin" then come and speak to us about having your own dedicated on-site HSMs backed by our infrastructure.
Recommended content:
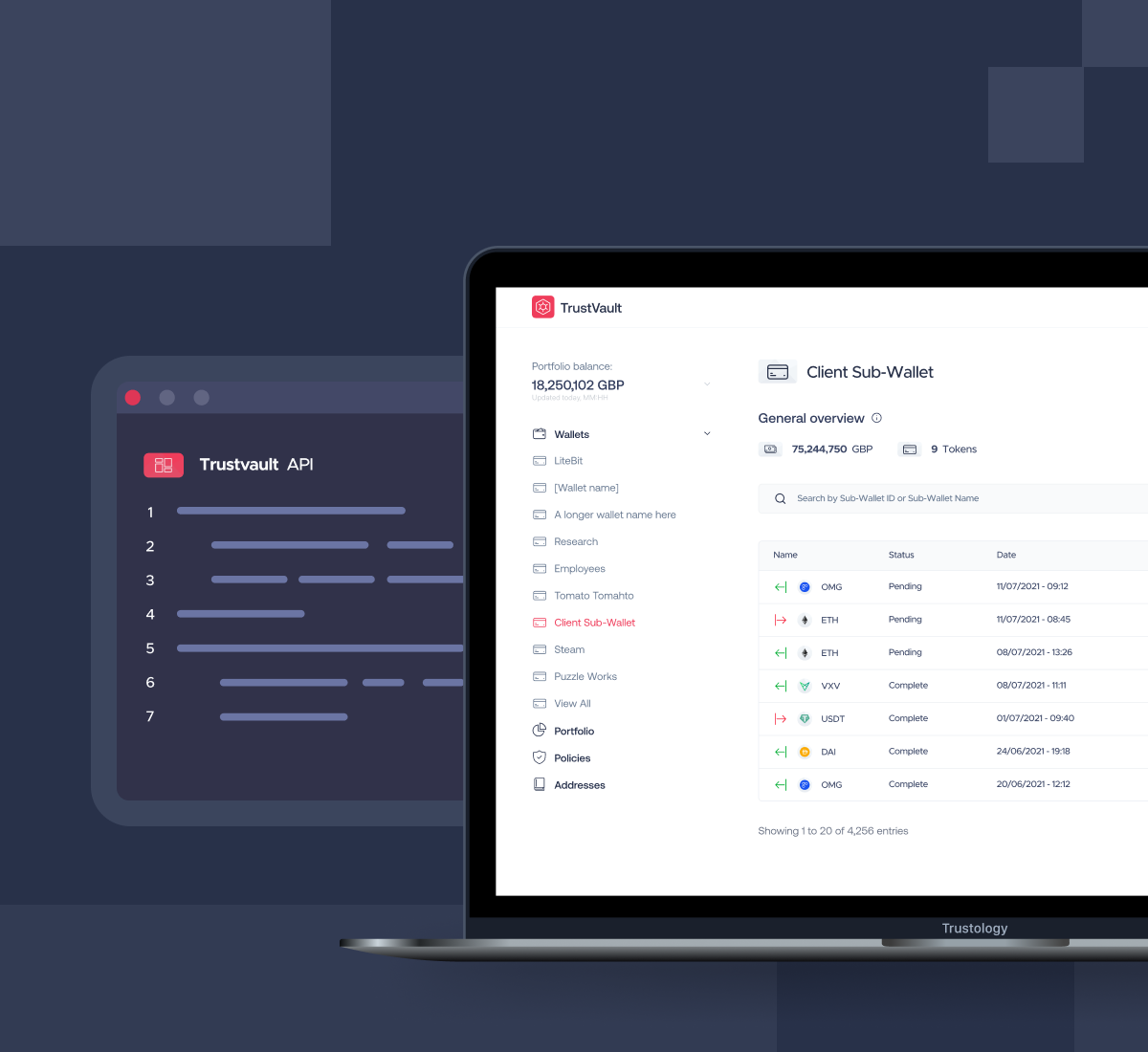
Securely trade, lend, borrow or hedge with DeFi and TrustVault custody

